Technology has evolved over time and so have the risks that surround it. Though businesses have been embracing innovative security approaches, the threat posed by cyber attackers and fraudsters continues to exist.
Not just cyber-attacks but data, when exposed to a large number of users, tends to be misused or meddled with.
Data security concerns extend to cloud systems as well. There exists a myth that because data on the cloud is available on a unified platform, it becomes easier for fraudsters to hack a cloud-based system.
However, in reality, cloud service providers adhere to stringent security practices and conduct high-end patch management to maintain data security.
Yet another way cloud services providers overcome this hurdle is by implementing strong security authorisation techniques. This can be as simple as protecting data with a password or implementing role-based access.
And now, with increasing cyber threats, cloud telephony providers have begun to look for enhanced security best practices. One among these is the two-factor authentication technique.
So, what is two-factor authentication and how can cloud telephony providers use it to safeguard data? Let us break it down for you.
What is two-factor authentication?
As the term suggests, the two-factor authentication technique prompts you to enter additional sets of credentials to access protected data. So, if you have a username and password to safeguard sensitive information on the cloud, you will need to enter another layer of credentials like a One-Time Password (OTP).
In short, the implementation of two-factor authentication adds an additional layer of safety to your already secured data on the cloud.
How do you implement two-factor authentication?
Authentication techniques are plenty––they can be two-factor or even multi-factor. They range from obtaining an OTP on your registered mobile number to using biometrics to access information. Some of them are:
-
SMS 2FA
Here, the system sends a security code to the registered mobile device via an SMS. You are expected to enter this code into the system to access information.
-
TOTP 2FA
The time-based one-time password is a password key that is generated on the device you are using to access the information—usually a barcode. You will simply need to scan this code using your device within the valid duration.
-
Pushed-Based 2Fa
You are asked to authenticate your identity through mobile-based notifications. When you prove your identity, you are provided access to the data.
-
U2F Tokens
U2F tokens come as USB ports. You can simply insert them into your device and press a button located on the top of the port. This prompts a credential request. Once you enter the information, you are provided access to the desired data.
Why is two-factor authentication important?
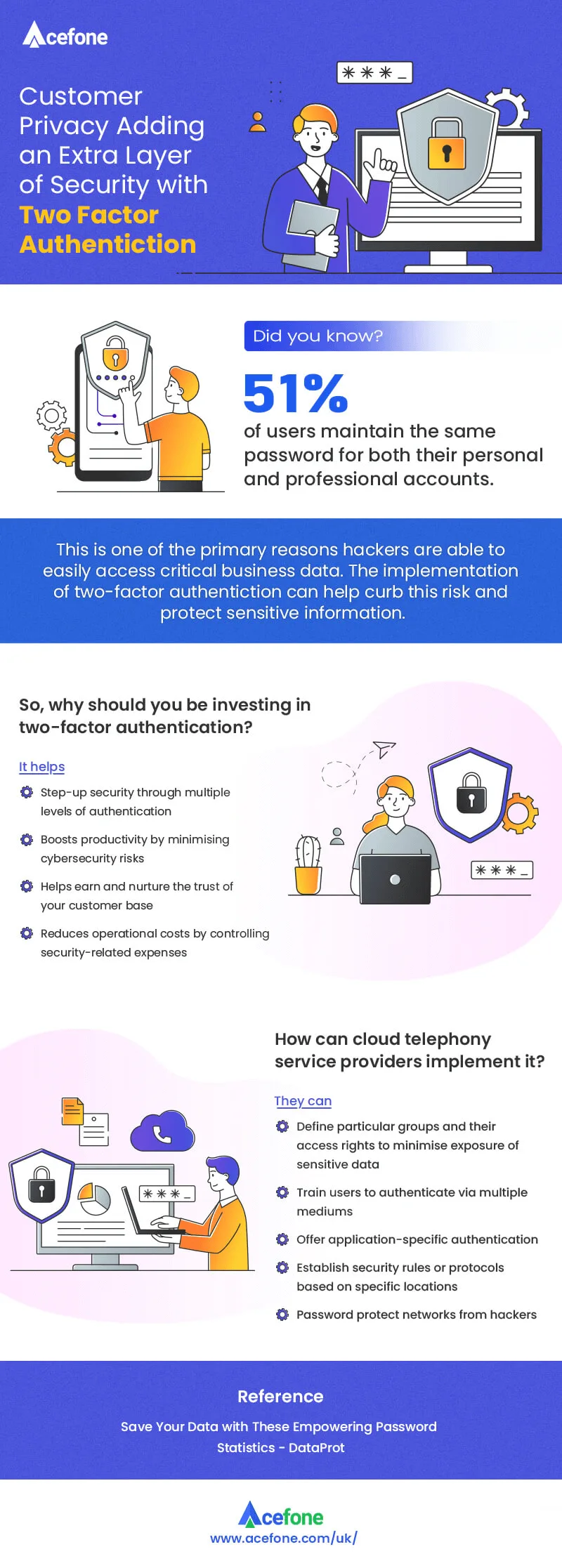
The worldwide information security market is estimated to reach $170.4 billion in 2022. Yet, approximately 68% of business leaders feel cybersecurity risks are increasing.
When we say two-factor authentication, it refers to appropriate authentication through two completely different channels.
For example, consider you are trying to access some information. You enter your login credentials over the Internet. The chances of a cyber-attacker hacking your network and stealing your credentials are high.
With two-factor authentication in place, you are expected to enter another set of credentials. This may be a code that you get on your mobile or a barcode you need to scan. So, even if an attacker obtains access to your credentials, they will not be able to get a hold of your mobile device and vice versa.
Therefore, two-factor authentication plays a cardinal role in safeguarding your data from phishing attacks, brute force attacks, and exploitation of weak login credentials.
With this brief, let’s now look into how beneficial two-factor authentication is and how effectively can cloud telephony service providers implement it.
-
Boosts security
When you incorporate two different ways of authenticating the user, it automatically steps up your data security level. You ensure that any important information isn’t compromised, no matter what.
-
Improves productivity
When data is secured by two-factor authentication, you can access business-critical information from anywhere across the globe on a unified cloud platform. With remote work becoming the new normal, you can rest assured that all your information is safe from hackers and cyber-attacks. This boosts accessibility and productivity.
-
Builds trust and reputation
When you secure data and maintain its integrity, you prevent cyber-attacks. This induces trust amongst your client base. They feel relieved that they are in association with a trustworthy service provider, thereby enhancing your reputation.
-
Lowers operational costs
The implementation of two-factor authentication boosts security. This, therefore, lowers the costs that go into addressing recurring security issues. It also reduces the burden of having to deal with an incident and therefore, lowers operational costs drastically.
So, how do cloud telephony service providers offer this security feature?
As cloud telephony service providers, you can adhere to just one (or many) of these approaches to implement two-factor authentication.
-
Secure specific users or groups
Try providing 2FA to particular groups and users based on their roles and responsibilities. That is, your employees or users will be provided access to data that is required to only complete their work-related tasks. This limits the exposure of data, thereby keeping it safe.
-
Authenticate using different methods
You can try using a mix-and-match of two-factor authentication techniques to protect data. That is, you can safeguard a specific group using push authentication and another group using OTPs. This way, you ensure your employees are equipped with the best security strategy.
-
Protect based on application
If your business processes involve sensitive applications, you can consider protecting these specific applications using high-end security authentication techniques like TOTP or push notifications.
-
Lay security rules based on geographical location
If a certain group of users is working remotely from a particular location, you can reinforce 2FA techniques for this geography.
-
Safeguard your network
You can also secure users based on their network. Home or public networks should ideally have an additional layer of security. They’re more prone to cyber attacks as they can easily be tampered with. Therefore, you must have strict security practices in place for employees to follow.
In a nutshell
The rate at which sensitive business data is being compromised has left several businesses in a panic. The need of the hour is to implement robust data safety measures. Two-factor authentication is one of the many ways to protect your sensitive information from fraudsters.